CoDefender 1.2.281
CoDefender security software is built on our (U.S. and international) ... and is an essential component of a complete security solution:
* Defense in Depth - Provides an extra layer of security.
* Last Line of Defense - Provides protection even when your existing security solutions, such as anti-virus and anti-spyware programs, have been compromised.
* Anti-keylogging Protection - Protects against user-level ...
| Author | Encassa |
| License | Trialware |
| Price | $25.17 |
| Released | 2009-06-24 |
| Downloads | 301 |
| Filesize | 5.45 MB |
| Requirements | Microsoft® .NET Framework 2.0 |
| Installation | Instal And Uninstall |
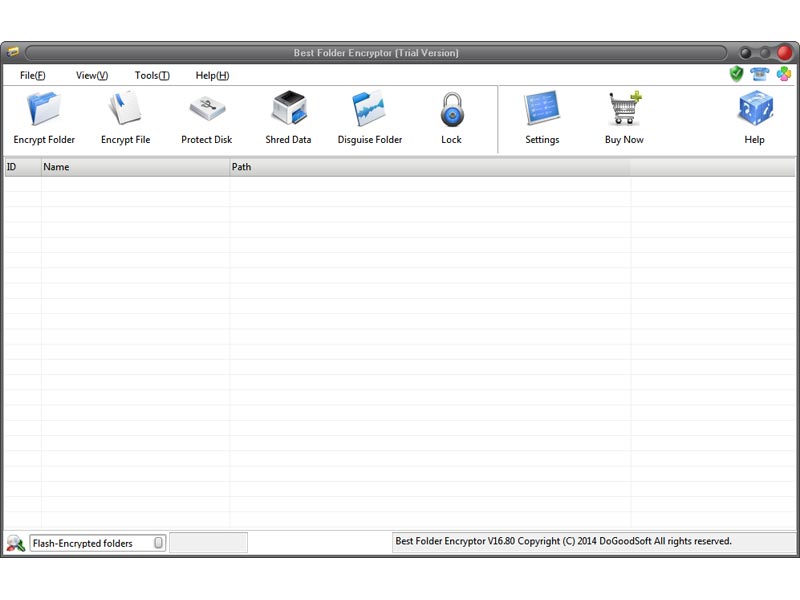
| Keywords | security, privacy, encrypt, encryption tool, protection |
| Users' rating (30 rating) |
Using CoDefender Free Download crack, warez, password, serial numbers, torrent, keygen, registration codes,
key generators is illegal and your business could subject you to lawsuits and leave your operating systems without patches.
We do not host any torrent files or links of CoDefender on rapidshare.com, depositfiles.com, megaupload.com etc.
All CoDefender download links are direct CoDefender full download from publisher site or their selected mirrors.
Avoid: security log oem software, old version, warez, serial, torrent, CoDefender keygen, crack.
Consider: CoDefender full version, security log full download, premium download, licensed copy.